Tenable OT Security, formerly known as Tenable.ot, brings hybrid discovery capabilities and increased visibility for the broadest range of IT and OT devices, making it easier than ever for CISOs to manage security and risk.
Security teams working in environments that rely on operational technology (OT) — including oil and gas, manufacturing and other critical infrastructure sectors — often find themselves challenged to get full visibility. Yet, it's essential for them to know what devices are out there, and the context in which these devices operate. Today, we announced a new release of Tenable OT Security designed to maximize value for the CISO’s team and OT operators, giving them the visibility they need to secure their OT environments. The goal? To make it easier than ever for IT security teams to govern connected operational technology (OT) environments using the same tools and processes across their entire infrastructure — be it cloud, internet of things (IoT), OT or other platforms.
What’s inside Tenable OT Security?
New features and capabilities in Tenable OT Security include:
In-depth asset visibility
Network segmentation is a security best practice in OT environments, however, it reduces visibility. How do you secure what you can’t see? Tenable OT Security overcomes this challenge with active sensors that can be deployed deep within network segments, sniffing packets to identify the devices communicating on the wire. Once there is an inventory of the assets on the network, Tenable OT Security sends active queries in a safe and secure manner to discover the remaining dormant devices. This is called hybrid discovery and Tenable is the first to use this methodology for effective asset inventory and mapping. Security teams can now get visibility into device make and model, as well as firmware version and status, and map the device’s connections to others on the network.
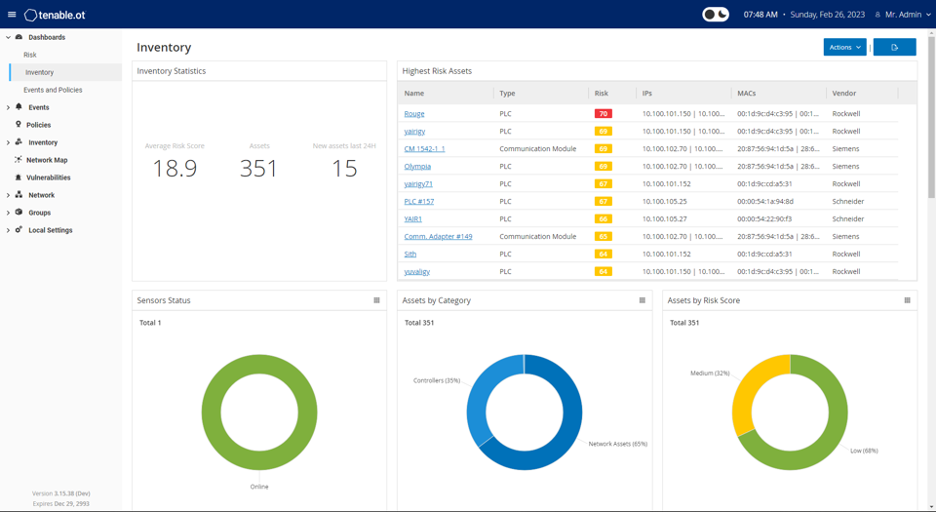
Source: Tenable, March 2023
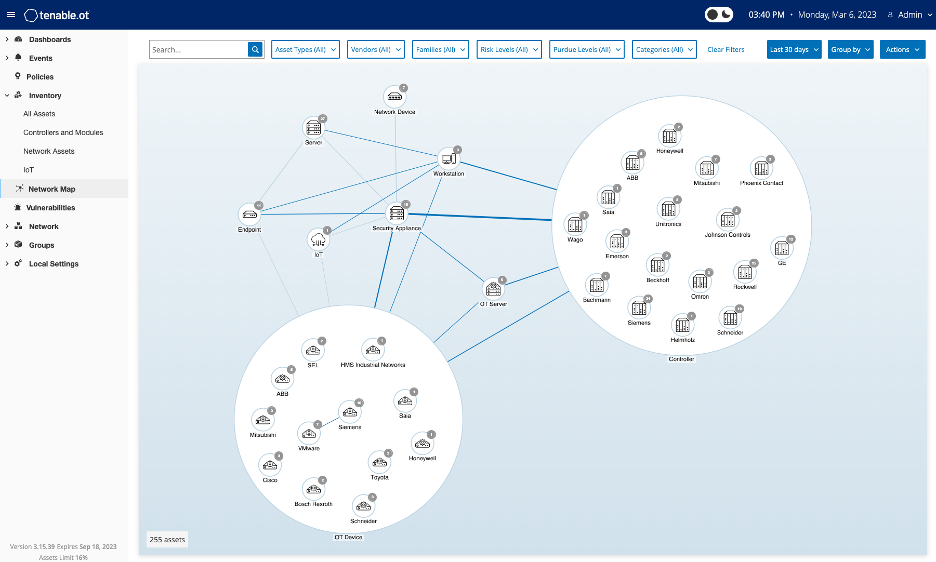
Source: Tenable, March 2023
Tenable OT Security has the most coverage of OT vendors and protocols in the market and continues to build on that with this release. We have added support for:
- Phoenix Contact: PCWORX and ProConOS protocols
- Profinet CM Context Manager
- Rockwell Automation L8X Family
- Bosch PSI Controllers
- Bachmann M1
Advanced vulnerability and threat detection
OT environments have a mix of IT and OT devices, including workstations, servers, human-machine interfaces (HMIs), historians, programmable logic controllers (PLCs), remote terminal units (RTUs), intelligent electronic devices (IEDs) and network devices. But having visibility of OT devices on the network is only half the picture.
Tenable OT Security now has the latest version of Nessus embedded into its user interface, bringing the industry standard for IT vulnerability assessment into the leading OT security solution on the market. Nessus is used specifically for IT devices on the OT network, enabling users to perform high-speed asset discovery, target profiling, configuration auditing, malware detection and sensitive data discovery.
Tenable OT Security leverages multi-detection methodologies to identify anomalous network behavior, monitors network security policies and tracks local changes on devices. In this release, the built-in intrusion detection system (IDS) engine gets a major improvement in order to detect the latest threats in the wild. The process to update IDS rules is now automated and allows users to create custom rules in order to detect suspicious activities and generate alerts that can be forwarded to your security operations center’s (SOC) security information and event management (SIEM) and security orchestration, automation and response (SOAR) solutions to enable automated responses and deeper investigations.
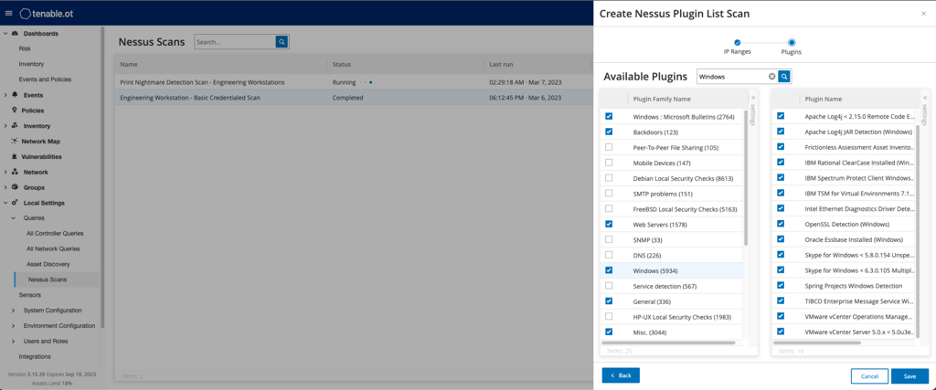
Source: Tenable, March 2023
Enhanced dashboarding and reporting
Managing visibility and security across multiple sites can be difficult. There needs to be a view of all site data on a single screen without the data becoming difficult to interpret. Tenable OT Security’s new dashboards provide a centralized view of distributed sites, featuring dozens of user-configurable widgets that make the data easy to consume and communicate. All of the dashboards can quickly and easily be exported as PDF reports and shared with all key stakeholders. Some of the new dashboard widgets are:
- Most common vulnerabilities
- Most common plugin families
- Most severe vulnerabilities
- Most common policies
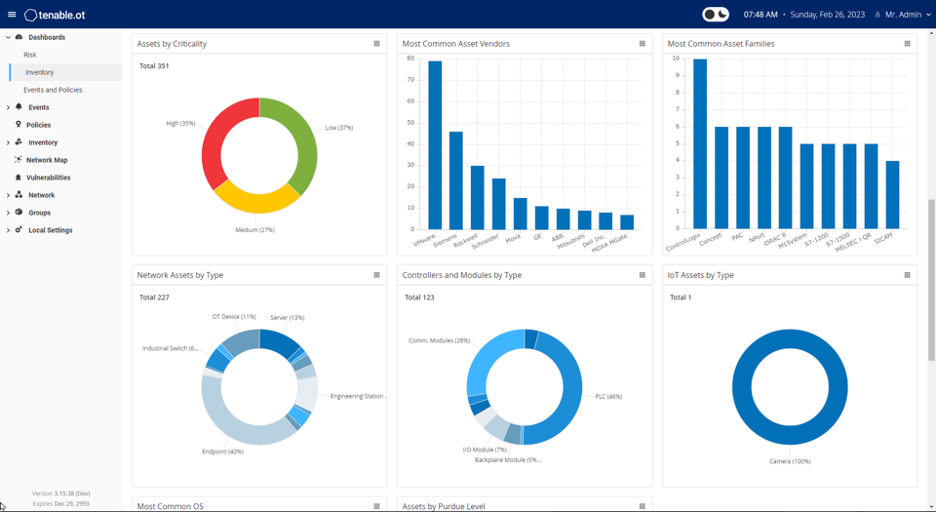
Source: Tenable, March 2023
In addition, a new darkmode feature makes it more comfortable to view the dashboards in low-light situations and offers a sleek interface when working in Tenable OT Security.

Source: Tenable, March 2023
Protection for the entire attack surface
In order to reduce cyber risk, security teams need to break down interdepartmental silos. However, defense-in-depth strategies have led to tool and alert fatigue, as well as low adoption rates of tools that don’t facilitate collaboration. According to a Gartner® Press Release, “Security and risk management leaders are increasingly dissatisfied with the operational inefficiencies and the lack of integration of a heterogeneous security stack.”1 Tenable continues to invest in a technology stack with robust integrations. Tenable OT Security, Tenable Vulnerability Management (formerly Tenable.io) and Tenable Security Center (formerly Tenable.sc) work together to increase cross-functional collaboration. Trusted for 25 years, Tenable is the only cybersecurity company that can provide customers with the breadth of solutions and depth of experience to defend against the current and complex attack surface.
The above is only a partial list of the new features in Tenable OT Security. To get all the details on what’s new and improved, please see our latest release notes.
And don’t delay upgrading to the latest version of Tenable OT Security. Get a jump on the new year and start fresh with everything that Tenable OT Security has to offer.
Schedule your free consultation and demo
Want to see what Tenable OT Security can do for your organization? Schedule a free consultation to check out a demo of Tenable OT Security and discuss how we can help you improve your security program and results.
For more information about Tenable OT Security, visit www.tenable.com/products/tenable-ot or view the video below:
1Gartner, Gartner Survey Shows 75% of Organizations Are Pursuing Security Vendor Consolidation in 2022, September 13, 2022. https://www.gartner.com/en/newsroom/press-releases/2022-09-12-gartner-survey-shows-seventy-five-percent-of-organizations-are-pursuing-security-vendor-consolidation-in-2022. GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Learn more
- Read the press release: Tenable Bolsters Tenable OT Security to Deliver the Broadest Security Coverage for Critical Infrastructure Environments
- View the webinars:
- Download the Forrester Wave Report for Industrial Control Systems (ICS) Security Solutions
- Visit the Tenable OT Security product page:https://www.tenable.com/products/tenable-ot
