More than 40% of ransomware attacks last year impacted critical infrastructure. Plus, a survey shows how artificial intelligence is impacting cybersecurity jobs. Meanwhile, MITRE updated a database about insider threats. And why you need a custom compensation strategy to recruit cyber pros. And much more!
Dive into six things that are top of mind for the week ending March 8.
1 - FBI: Critical infrastructure walloped by ransomware attacks in 2023
The number of U.S. ransomware incidents grew 18% in 2023 to 2,825, and 42% of those attacks impacted critical infrastructure organizations. LockBit, ALPHV/Blackcat, Akira, Royal and Black Basta ranked as the most prevalent ransomware variants affecting critical infrastructure.
That’s according to the “2023 Internet Crime Report” which was released this week by the FBI’s Internet Crime Complaint Center (IC3) and also found that healthcare was the hardest hit among critical infrastructure sectors, with 249 reported attacks.
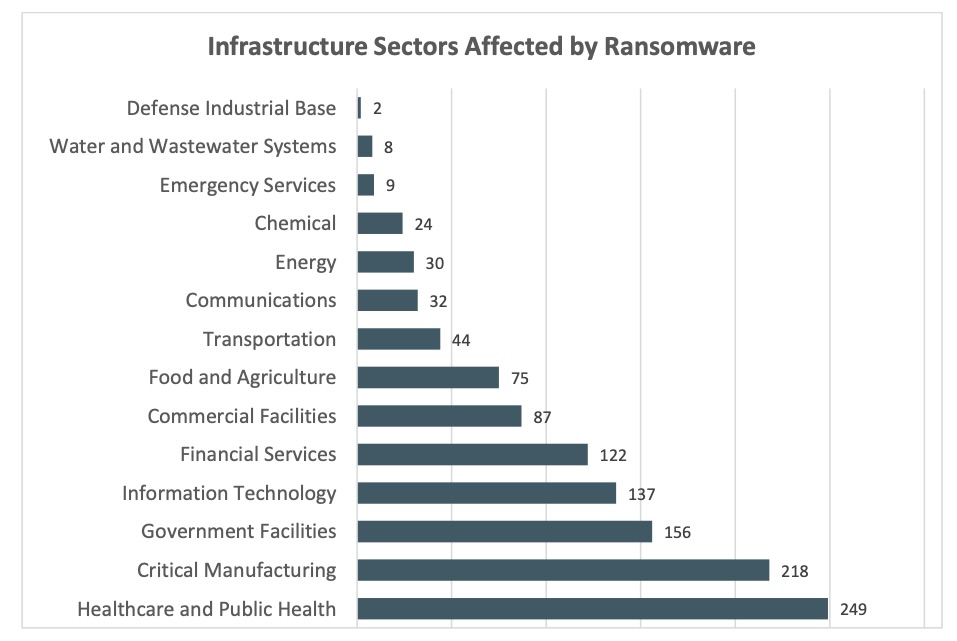
(Source: “2023 Internet Crime Report” from the FBI’s Internet Crime Complaint Center, March 2024)
Overall, ransomware losses skyrocketed 74% to almost $60 million, as attackers employed new tactics, such as pelting victims with multiple ransomware variants.
Looking at cybercrime in general, individuals and businesses in the U.S. lost $12.5 billion, a hefty 22% jump over 2022. The number of cybercrime complaints grew almost 10% to 880,000.
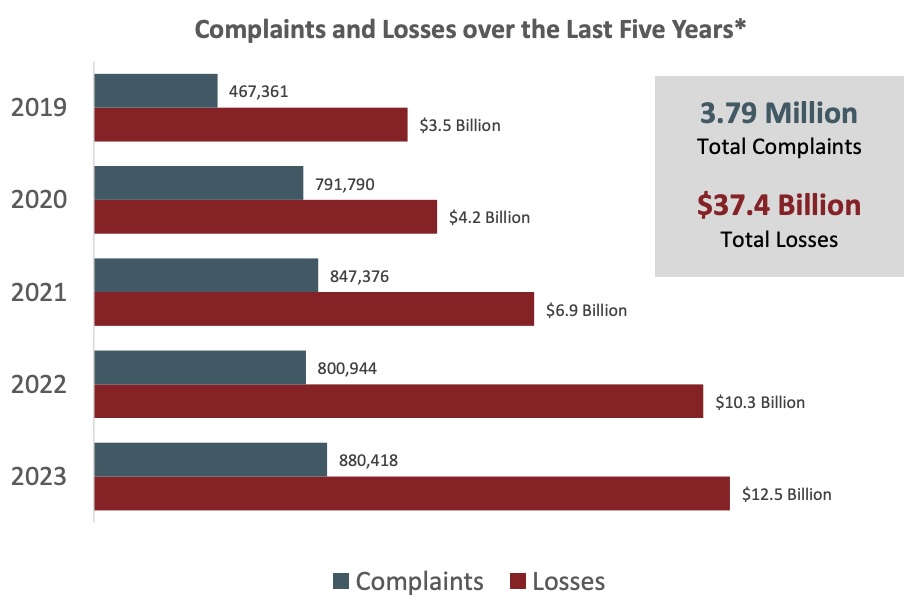
(Source: “2023 Internet Crime Report” from the FBI’s Internet Crime Complaint Center, March 2024)
Those are big numbers, but the FBI calls them “conservative” because many incidents go unreported. An example: When the FBI recently infiltrated the Hive ransomware group’s infrastructure, it found that only about 20% of Hive's victims had filed a law enforcement report.
Meanwhile, investment fraud topped all crime categories with investment scams losses rising 38% to $4.57 billion. Business email compromise (BEC) ranked second with $2.9 billion in losses.
For more information about cybercrime trends:
- “3 trends set to drive cyberattacks and ransomware in 2024” (World Economic Forum)
- “Cybercrime Expected To Skyrocket in Coming Years” (Statista)
- “Cybersecurity 101: Everything on how to protect your privacy and stay safe online” (ZDNet)
- “Disruptive new wave of ransomware hits critical infrastructure” (Axios)
- “Critical Infrastructure Orgs Must Beware of China-backed Volt Typhoon” (Tenable)
VIDEOS
Tenable CEO Amit Yoran Discusses Ransomware Attack on UnitedHealthcare (CNN)
Homeland Security Testimony 2024: Funding critical infrastructure and secure by design (Tenable)
Ransomware in OT Systems (Tenable)
2 - Survey: AI transforming cybersecurity work
Artificial intelligence, including generative AI, has started substantially changing how cybersecurity professionals work – both in positive and negative ways.
That’s according to ISC2’s survey “AI in Cyber 2024: Is the Cybersecurity Profession Ready?”, based on a poll of 1,123 cybersecurity pros.
Key findings include:
- 88% of cybersecurity pros polled said they expect AI to “significantly impact” their roles and tasks over the next couple of years
- 35% said AI is already reshaping how they perform their daily jobs
- 56% expect AI to make at least some parts of their jobs obsolete
- 82% forecast AI will make them more efficient at work
The chart below shows where respondents expect AI to improve their efficiency.
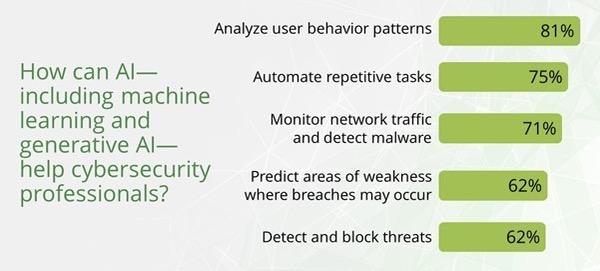
(Source: “AI in Cyber 2024: Is the Cybersecurity Profession Ready?” from ISC2, February 2024)
These tasks are lower-value, time-consuming functions, meaning AI is unlikely to replace cyber pros, but rather free them up to focus on complex, higher-value tasks, the ISC2 said in its article about the survey “The Real-World Impact of AI on Cybersecurity Professionals.”
“There is no doubt that AI is going to change and redefine many cybersecurity roles, removing people from certain high-speed and repetitive tasks, but is less likely to eliminate human cybersecurity jobs completely,” reads the article.
Respondents also voiced concerns about AI, including:
- Its use by cybercriminals for malicious purposes, such as:
- deepfakes, cited by 76% of respondents
- disinformation campaigns (70%)
- social engineering (64%)
- Regulatory, ethical and privacy issues, such as:
- a lack of regulation (59%)
- ethical violations (57%)
- privacy invasion (55%)
Also of concern is that many organizations are adopting AI without having a usage policy in place to ensure it’s used safely, legally and responsibly. Specifically, only 27% of respondents said their organizations have a policy for using AI safely and ethically, and only 15% have a policy for securing and deploying AI.
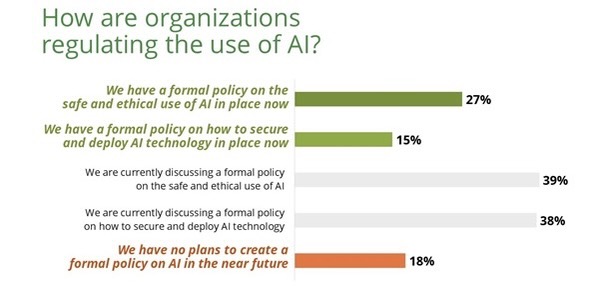
(Source: “AI in Cyber 2024: Is the Cybersecurity Profession Ready?” from ISC2, February 2024)
For more information about the use of AI by cybersecurity teams:
- “GenAI Drives Broader Use of Artificial Intelligence Tech for Cyber” (Tenable)
- “Evaluate the risks and benefits of AI in cybersecurity” (TechTarget)
- “The role for AI in cybersecurity” (Cybersecurity Dive)
- “AI Is About To Take Cybersecurity By Storm” (Tenable)
- “New Generative AI Tools Aim to Improve Security” (Dark Reading)
VIDEO
Tenable CEO Amit Yoran discusses AI and preventive security (CNBC)
3 - U.S.: Phobos ransomware hitting critical infrastructure, emergency services
And we’re returning to the topic of how ransomware gangs have their sights set on critical infrastructure targets.
The FBI, the Cybersecurity and Infrastructure Security Agency (CISA) and the Multi-State Information Sharing and Analysis Center (MS-ISAC) are advising U.S. local governments to act immediately to lower the risk of falling victim to the Phobos ransomware-as-a-service operation.
In the joint advisory “#StopRansomware: Phobos Ransomware,” the agencies said that since May 2019, Phobos has targeted state, local, tribal and territorial governments, disrupting emergency services, critical infrastructure facilities, public healthcare organizations and more.

The new joint advisory includes Phobos tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) observed as recently as February 2024, along with recommended mitigations.
Steps that cybersecurity teams should take as soon as possible include:
- Secure Remote Desktop Protocol (RDP) ports and strictly limit the use of RDP and other remote desktop services by, for example:
- Closing unused RDP ports
- Applying phishing-resistant multi-factor authentication (MFA)
- Logging RDP login attempts, and locking out accounts after a pre-determined number of login attempts
- Prioritize the remediation of known exploited vulnerabilities
- Adopt application controls and specifically allowlist remote access programs to prevent attackers from installing their own remote access tools
4 - MITRE adds mitigations to Insider Threat TTP KB
If you use MITRE’s “Insider Threat TTP Knowledge Base,” there’s news to share: This comprehensive collection of insider-threat TTPs has been enhanced and expanded.
What’s new? For starters, version 2.0 of the “Insider Threat TTP Knowledge Base” now includes mitigation recommendations for each one of the techniques in the database.

The most common mitigations included are foundational practices, such as account management, multi-factor authentication, auditing, and disabling or removal of features or programs.
“These demonstrate that basic cyber hygiene is still essential and effective when designing a security program,” wrote Mike Cunningham and Suneel Sundar from MITRE Engenuity’s Center for Threat-Informed Defense in the blog “Insider Threat Knowledge Base 2.0.”
Also new in version 2.0 are additional techniques, as well as observable human indicators (OHI), which are attributes of individuals, such as their job title and access level, that can be used to factually assess their potential to be an insider threat risk.
For more information about insider cyberthreats:
- “Insider threats surge across US critical infrastructure as attackers exploit human factors” (CSO)
- “Top 10 Insider Threats” (OWASP)
- “Why employees are a bigger security risk than hackers” (Raconteur)
5 - Study: Cyber recruiting requires custom compensation strategy
As has been well documented, finding qualified candidates to fill cybersecurity jobs is a challenge, as demand vastly exceeds supply.
Given the difficulty in recruiting and retaining cybersecurity pros, CISOs and their hiring managers must get their compensation strategy right. A big part of that is understanding that they can’t rely on a conventional approach to compensation.
That’s according to IANS Research and Artico Search, which just published their “2023-2024 Cybersecurity Staff Compensation Benchmark Report,” based on a poll of 560-plus cyber pros in the U.S. and Canada.
“Comprehensive, infosec-specific compensation data is critical for benchmarking, as recruiting in security often requires specialized compensation packages to compete for talent and minimize attrition,” the firms said in the blog “Key Infosec Staffing Insights.”
One particularity, as the report found, is that cybersecurity staffers often wear multiple hats, so one person may be involved in application security (AppSec); product security; and identity and access management.
The chart below shows the percentage of cybersecurity pros that support more than one functional area. For example, among those whose primary role is security operations (SecOps), 39% are also involved in governance, risk and compliance (GRC); 47% in architecture and engineering (A&E); and 31% in AppSec.
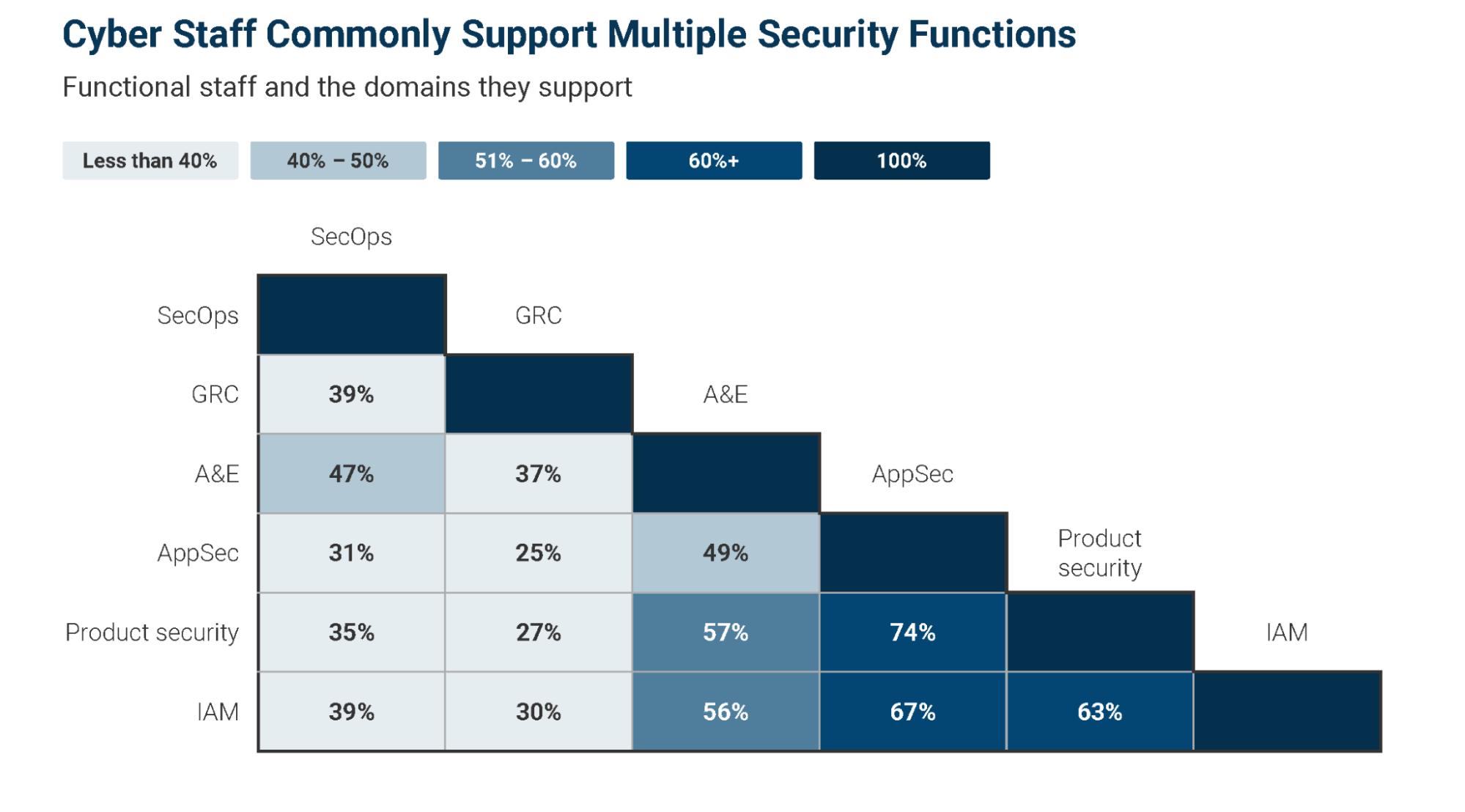
(Source: “2023-2024 Cybersecurity Staff Compensation Benchmark Report” from IANS Research and Artico Search, February 2024)
“We advise CISOs review the responsibilities and functional overlap of roles within their organization to determine how they align with those of other companies,” the blog reads.
For more information about cybersecurity salary trends:
- “Top-paying cybersecurity jobs and salary trends for 2024” (Infosec)
- “CISO salaries are up, but growth is slowing” (Cybersecurity Dive)
- “Cybersecurity Salary Guide: How Much Can You Earn?” (Forbes)
6 - White House urges use of memory-safe coding languages
The White House is pleading with software and hardware makers to use memory-safe programming languages, arguing that doing so will help reduce pervasive memory vulnerabilities that cyberattackers frequently leverage.
Memory safety bugs can allow hackers to maliciously manipulate how memory is accessed, written, allocated or deallocated, according to the White House’s “Back to the Building Blocks: A Path Toward Secure and Measurable Software” report.
“Building new products and migrating high-impact legacy code to memory safe programming languages can significantly reduce the prevalence of memory safety vulnerabilities throughout the digital ecosystem,” reads the report. It identifies C and C++ as memory-unsafe languages.

The report echoes a call that cybersecurity agencies from multiple countries, including the U.S., made in December when they jointly published “The Case for Memory Safe Roadmaps” guide, which listed C#, Go, Java, Python, Rust and Swift as memory-safe languages.
The White House report, created by the Office of the National Cyber Director (ONCD), also calls for the development of better diagnostic metrics to measure software products’ cybersecurity quality.
To get more details about the White House initiative, check out:
- The announcement “Future Software Should Be Memory Safe”
- The 19-page report “Back to the Building Blocks: A Path Toward Secure and Measurable Software”
- The fact sheet “ONCD Report Calls for Adoption of Memory Safe Programming Languages and Addressing the Hard Research Problem of Software Measurability”
- This video from the ONCD director and assistant director
For more information about memory safe programming languages:
- “The Move to Memory-Safe Programming” (IEEE Spectrum)
- “Shift to Memory-Safe Languages Gains Momentum” (Dark Reading)
- “Efforts to improve memory safety in software gain momentum” (TechTarget)
- "Automated Code Repair to Ensure Memory Safety" (Software Engineering Institute, Carnegie Mellon Univ.)
