CISA’s red team acted like a nation-state attacker in its assessment of a federal agency’s cybersecurity. Plus, the Cloud Security Alliance has given its cloud security guidance a major revamping. Meanwhile, a Google report puts a spotlight on insecure credentials. And the latest on open source security, CIS Benchmarks and much more!
Dive into six things that are top of mind for the week ending July 19.
1 - CISA’s red team breaches fed agency, details lessons learned
A new, must-read report from the U.S. Cybersecurity and Infrastructure Security Agency (CISA) outlines how the agency’s red team probed a large federal agency’s network, quickly found a way in and stayed undetected for months.
The 29-page report details the so-called SilentShield assessment from CISA’s red team, explains what the agency’s security team should have done differently and offers concrete recommendations and best practices you might find worth reviewing.
Mimicking the modus operandi of a typical nation-state attacker, CISA’s red team exploited a known vulnerability on an unpatched web server, gaining access to the agency’s Solaris environment. Separately, the red team also breached the network’s Windows environment via a phishing attack.

Once inside, the red team was able to exploit other weaknesses, such as unsecured admin credentials, to extend the scope of the breach, which went undetected for five months. At that point, CISA alerted the agency about the SilentShield operation.
CISA has authorization to conduct SilentShield assessments, whose purpose is to work with the impacted agency and help its security team strengthen its cyberdefenses.
Here’s a brief sampling of the assessed agency’s security weaknesses:
- Lack of sufficient prevention and detection controls, including an inadequate firewall between its perimeter and internal networks; and insufficient network segmentation
- Failure to effectively collect, retain and analyze logs, which hampered defensive analysts’ ability to gather necessary information
- Bureaucratic processes and siloed teams
- Reliance on flagging “known” indicators of compromise (IOCs) instead of using behavior-based detection
- Lack of familiarity with the identity and access management system (IAM), which wasn’t tested against credential-manipulation techniques nor were its anomalous-behavior alerts monitored
Recommendations include:
- Deploy internal and external firewalls
- Implement strong network segmentation
- Enroll all accounts in the IAM system, and make sure it’s not vulnerable to credential manipulation
- Centralize logging and use tool-agnostic detection
To get more details, read the report, titled “CISA Red Team’s Operations Against a Federal Civilian Executive Branch Organization Highlights the Necessity of Defense-in-Depth.”
For more information about the threat from nation-state cyberattackers:
- “What CISOs Need to Know About Nation-State Actors” (InformationWeek)
- “4 Ways to Defend Against Nation-State Attacks” (BankInfoSecurity)
- “Growing Nation-State Alliances Increase U.S. Cyber Risks” (Government Technology)
- “Nation-State Hackers Leverage Zero-Day Vulnerabilities to Penetrate MITRE Cybersecurity Research Network” (CPO Magazine)
2 - Cloud Security Alliance’s cloud sec guide gets revamped
The Cloud Security Alliance (CSA) has given a major makeover to its “Security Guidance for Critical Areas of Focus in Cloud Computing,” including adding new topics like artificial intelligence (AI), and boosting coverage of areas like data security and IAM.
The guide is aimed at helping organizations understand cloud computing components and cloud security best practices. Version 5, released this week, replaces version 4, which was published in 2017.
“We have completely revamped this updated 5th version to align with modern technologies and challenges,” reads the CSA blog “New Cloud Security Guidance from CSA.”

Here’s some of what’s new:
- Increased coverage of cloud workloads, application security, CI/CD, data security and DevSecOps
- New topics such as AI and zero trust
- Less emphasis on laws and regulations
The guide is organized into 12 sections, including:
- Cloud computing concepts and architectures
- Cloud governance and strategies
- Risk, audit and compliance
- IAM
- Cloud workload security
- Data security
For more information about cloud security, check out these Tenable resources:
- “Tag, You’re IT! Tagging Your Way to Cloud Security Excellence” (blog)
- “Leveraging CIEM to Secure Cloud Identities and Entitlements at Scale” (on-demand webinar)
- “Understanding Customer Managed Encryption Keys in AWS, Azure and GCP” (blog)
- “Secure Your Cloud-Native Applications” (on-demand webinar)
- “Cloud Workload Protection: The Key to Decreasing Cloud Security Risks” (blog)
3 - Google: Credential gaps top initial-access vectors for cloud breaches
When it comes to gaining an initial foothold in a cloud environment, attackers’ best friends are weak or simply non-existent credentials. That’s according to the latest “Google Cloud Threat Horizons Report,” which is based on data gathered during the first half of 2024.
Specifically, weak or no credentials accounted for 47.2% of initial-access vectors in cloud compromises observed by Google Cloud in customer environments.
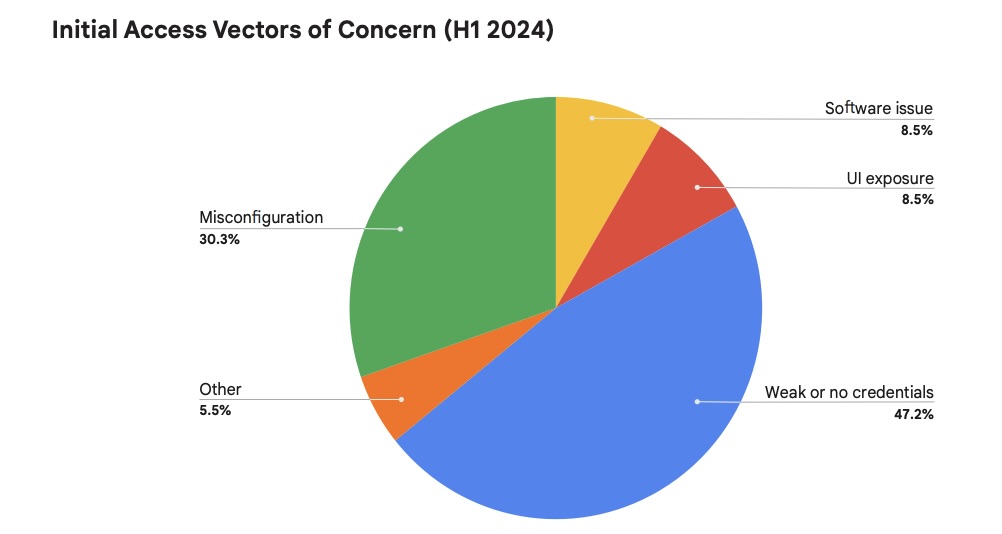
(Source: Google Cloud Threat Horizons Report, July 2024)
Meanwhile, using the compromised system for cryptomining ranked as attackers’ top intrusion motivation (58.8%).
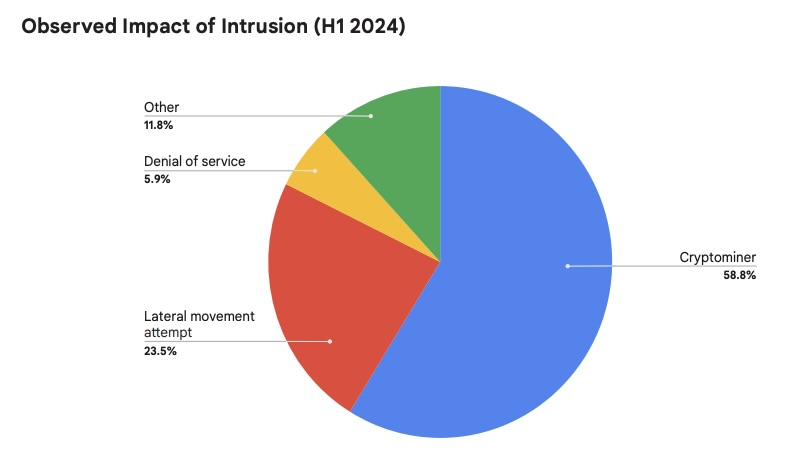
(Source: Google Cloud Threat Horizons Report, July 2024)
For more information about identity and access management security:
- “Poor Identity Hygiene at Root of Nation-State Attack Against Microsoft” (Tenable)
- “What is identity and access management? Guide to IAM” (TechTarget)
- “What is IAM? Identity and access management explained” (CSO)
- “Multifactor Authentication Is Not Enough to Protect Cloud Data” (Dark Reading)
4 - CISA working on OSS security framework, assessment tool
As part of its efforts to help improve the security of open source software (OSS), CISA is crafting a framework and backing the development of an automated tool for assessing whether an OSS component is trustworthy.
“As work on both the framework and supporting tools continue to progress, we will improve our capability to assess OSS trustworthiness at scale,” reads CISA’s blog “Continued Progress Towards a Secure Open Source Ecosystem.”
The assessment framework will evaluate four aspects of the development of an OSS component:
- Its project, including the number of active contributors and unexpected ownership changes
- The product, including whether it contains known vulnerabilities or outdated dependencies
- Its protections, such as whether developer accounts require MFA
- Its policies, such as requirements for code reviews and vulnerability disclosures
“Taken together, the collected measurements can be grouped into these four categories to provide software users and choosers a consistent way to evaluate the trustworthiness of a particular OSS component,” wrote blog author Aeva Black, CISA’s Section Chief of Open Source Software Security.
To automate the framework’s measurement process and combine the measurement results, CISA is funding the development of an open source tool called Hipcheck, which is designed to “automatically assess and score software repositories for supply chain risk,” according to its Github page.
For more information about open source software security:
- “Establishing a security baseline for open source projects” (Help Net Security)
- “OWASP Top 10 Risks for Open Source Software” (OWASP)
- “Create an open source security policy for your organization” (TechTarget)
- “How to Navigate Open-Source Security Without Stifling Innovation” (Infosecurity)
- “Study finds that SW developers lack cybersecurity skills” (Tenable)
5 - Banks get guidance on secure cloud adoption
Banks and other financial services institutions looking for fresh guidance on adopting cloud securely can check out new best-practices documents published this week.
The documents, published by the U.S. Treasury Department and the Financial Services Sector Coordinating Council (FSSCC) industry non-profit group, seek to accomplish goals such as:
- Establishing a common cloud-computing terminology for banks and regulators.
- Crafting best practices for reducing cloud-related third-party risk
- Improving transparency and monitoring of cloud services
- Creating a framework for cloud services adoption
“Today’s publications mark a significant step forward by providing a roadmap and helpful resources for banks of all sizes,” Acting Comptroller of the Currency Michael J. Hsu said in a statement. “These documents also clarify cloud service providers’ responsibilities for ensuring a secure and resilient financial system.”

To get more details, check out the Treasury’s announcement “Treasury and the Financial Services Sector Coordinating Council Publish New Resources on Effective Practices for Secure Cloud Adoption.”
For more information about cybersecurity in the financial sector:
- “The cyber clock is ticking: Derisking emerging technologies in financial services” (McKinsey)
- “A Cyber Defense Guide for the Financial Sector” (Center for Internet Security)
- “4 steps to secure your treasury operations from cyberattacks” (J.P. Morgan)
- “Global financial stability at risk due to cyber threats” (World Economic Forum)
- “The rise of cyberattacks on financial institutions highlights the need to build a security culture” (SC Magazine)
6 - CIS updates Benchmarks for Apple, Google, Red Hat products
Apple’s macOS. Microsoft’s Windows Server. Red Hat’s Enterprise Linux. Google’s Kubernetes Engine.
Those are among the products included in the latest round of updates for the popular CIS Benchmarks from the Center for Internet Security.
Specifically, these new secure-configuration recommendations were updated in June:
- CIS AlmaLinux OS 9 Benchmark v2.0.0
- CIS Apple macOS 12.0 Monterey Benchmark v3.1.0
- CIS Apple macOS 13.0 Ventura Benchmark v2.1.0
- CIS Apple macOS 14.0 Sonoma Benchmark v1.1.0
- CIS Google Kubernetes Engine (GKE) Benchmark v1.6.0
- CIS Microsoft Windows Server 2019 Stand-alone Benchmark v2.0.0
- CIS NGINX Benchmark v2.1.0
- CIS Oracle Linux 9 Benchmark v2.0.0
- CIS Red Hat Enterprise Linux 9 Benchmark v2.0.0
- CIS Red Hat OpenShift Container Platform Benchmark v1.6.0
- CIS Rocky Linux 9 Benchmark v2.0.0

In addition, CIS released brand new Benchmarks for AWS storage services, including Amazon Simple Storage Service (S3), and for Microsoft Azure database services, including Azure SQL.
Organizations can use the CIS Benchmarks’ secure-configuration guidelines to harden products against attacks. Currently, there are more than 100 Benchmarks for 25-plus vendor product families. Categories include cloud platforms; databases; desktop and server software; mobile devices; operating systems; and more.
To get more details, read the CIS blog “CIS Benchmarks July 2024 Update.” For more information about the CIS Benchmarks list, check out its home page, as well as:
- “Getting to Know the CIS Benchmarks” (CIS)
- “Security Via Consensus: Developing the CIS Benchmarks” (Dark Reading)
- “How to Unlock the Security Benefits of the CIS Benchmarks” (Tenable)
- “CIS Benchmarks Communities: Where configurations meet consensus” (Help Net Security)
- “CIS Benchmarks: DevOps Guide to Hardening the Cloud” (DevOps)
